
Data breaches and security incidents have become rampant across the social media sector, making continuous headlines. There are numerous incidents reported where unwitting users suffered frequent data and identity thefts, whose Facebook accounts were compromised.
Recently, a security research found cybercriminals selling the identities of 267 million Facebook users for £500 (US$623) on dark web forums. The exposed information includes email addresses, full names, last connection, status, age, phone numbers, Facebook IDs, birthdates, age, and other personal data, which could allow attackers to perform spear phishing or credential stuffing attacks.
By Rudra Srinivas, Senior Feature Writer, CISO MAG
Every suspicious activity on your Facebook account does not necessary mean that a hacker is behind it. If you can log into your account without any trouble, it means that your account is under your control and not compromised. If you are unable to login into your account, then you can expect potentially malicious intent. However, with proper security measures, users can safeguard their social media accounts from malevolent hands. In case you suspect your Facebook account is hacked, follow the below options to regain control of your account and for future protection:
When to React
Ask your Facebook friend to check your profile. Your account may be compromised if you find:
- Your name, profile picture, or email address have changed.
- If there are any new friends or friend requests to people you are unaware of.
- New posts on your timeline you did not posted.
Report the Hack
Though you are unable to access your account, you can regain control of your compromised Facebook account by reporting the hack to Facebook.
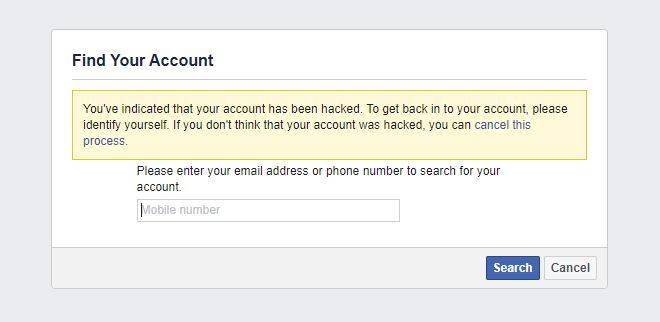
Visit Report Compromised Account page >> Select “My Account Is Compromised” option >> Enter your email ID or phone number linked to your account. The page displays a list of options. Select your reasons and follow the instructions.
Alert Your friends
Cybercriminals often use compromised accounts to spread fraudulent links or post distasteful or offensive comments. Inform your Facebook friends that your account has been compromised and ask them not to respond to any messages or links that they receive from your account.
Delete Suspicious Apps
Earlier, Facebook admitted that hundreds of users inadvertently gave access of their personal data to third-party apps. The affected users were also using their social media accounts to log in to certain applications.
Scrap all unknown and suspicious apps from your account. Hackers often use malicious applications to pilfer sensitive data, images, and other personal details from social media accounts.
Go to settings >> Click on Apps and Websites option >> Select the apps you want to remove
You can also delete all the data, photos, posts, and links shared through these apps. In addition, click the View and Edit option to change app permissions. You can limit the app’s access to your personal data.
Finally, Reset Security
Your account could be hacked again if no proper security measures are taken. Adhere to Facebook’s new security and privacy features. Enable two-factor authentication, which ensures that your account cannot be hacked with just one password. Use an authentication app like Google Authenticator for this.
About the Author
Rudra Srinivas is a Senior Feature Writer and part of the editorial team at CISO MAG. He writes news and feature stories on cybersecurity trends.
More from the Rudra.











