
Chat service provider WhatsApp and its competitors like Telegram have always maintained that their products provide end-to-end encryption (E2EE). But the recent turn of events around the globe has raised concerns about these claims. There is a widespread possibility that government and law enforcement organizations could be compromising E2E encrypted chat applications for viewing private data. While this is yet to be proven, a similar mechanism has given rise to a new severe vulnerability, which allows attackers to perform WhatsApp and Telegram account takeovers on its web platform.
The vulnerability, if exploited, would have given attackers access to the victims’ personal and group chats, photos, videos, other shared files, contact lists, and much more. In short, it could be a free pass for attackers in your personal space. They could download photos and sensitive data and demand a ransom in exchange for it. Attackers could also use the victims’ identity to further spread the attack and take over their friends’ accounts.
Related News:
WhatsApp vs Signal vs Telegram: Which is More Viable and Secure?
How the Vulnerability Worked
The vulnerability was first discovered by researchers from Check Point. They explained that the exploitation of the vulnerability began when the attacker sent a specially crafted image file to the victim containing a malicious code. The file could be modified to target the victim with a specific image or content that could interest the user in opening the attachment.
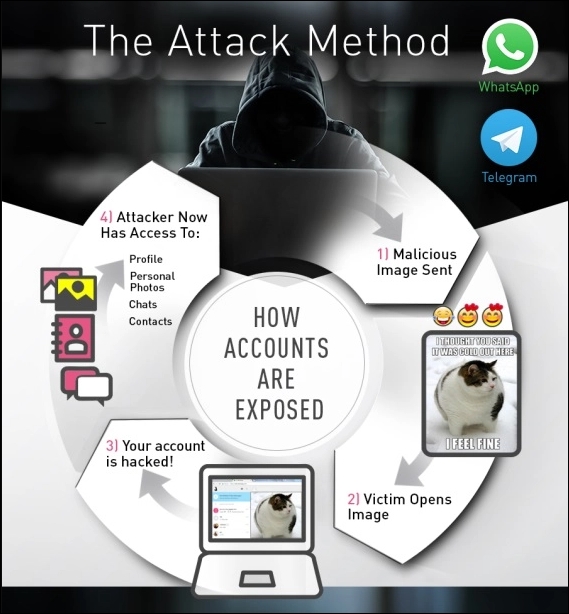
In WhatsApp, the exploitation of the vulnerability starts when the user clicks to open the image. The malicious code gets executed and allows the attacker free access into the victims’ local storage, where the data is stored. In Telegram, however, the user is required to click twice and open a new tab, for the attacker to access local storage. This leads the attacker to gain full access to the user’s account and data. The most dangerous part about this vulnerability is that it could have allowed the attacker to use victims’ contacts and potentially start an account takeover attack affecting both WhatsApp and Telegram.
It is Now Fixed!
Check Point researchers responsibly disclosed the vulnerability to both WhatsApp and Telegram’s security teams on March 7, 2020. Both companies verified and acknowledged the issue before developing a fix for all their web clients. Researchers recommended that WhatsApp and Telegram web users – who want to ensure if they are using the latest version – are advised to update and restart their browser. The fix gets auto-applied.










