Since the onset of the pandemic, crypto scammers have heightened their operations around the globe by targeting famed Twitter accounts for monetary gains. This time the Indian Prime Minister Narendra Modi is on the radar. Crypto scammers successfully hacked the verified Twitter account of the Indian PM’s official website and sent out a series of tweets asking its followers to donate towards the PM National Relief fund in cryptocurrency.

Key Highlights
- Indian Prime Minister Narendra Modi’s official website Twitter Account (@narendramodi_in) was hacked by crypto scammers claiming the name “John Wick”.
- The Twitter account in question has over 2.5 Million followers and posted over 37,000 tweets since its creation in May 2011.
- In a series of posts, the crypto scammers demanded donations from its followers towards the PM National Relief Fund in cryptocurrency.
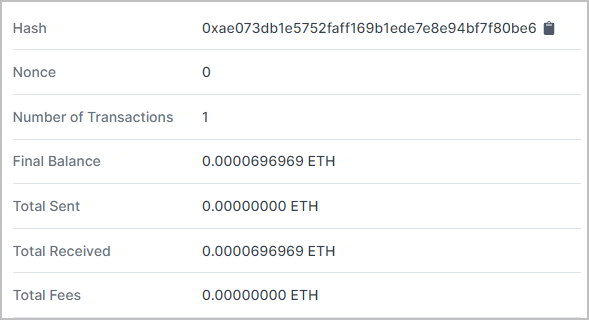
- Two cryptocurrency accounts, Bitcoin and Ethereum, have been used in the tweets to collect the donations.
- Twitter confirmed the account compromise and immediately took corrective measures to hand over the access controls back to its original administrator.
- Reportedly, the official website in question was also subsequently hacked but was later reinstated by its handlers.
Twitter, in a public statement, stated that it was aware of the (malicious) activity and has taken steps to secure the compromised accounts. Additionally, they also informed about the further investigations that are being carried out for identifying other impacts and compromises, if any.
Meanwhile, Twitter has already taken down the fake tweets and restored the account controls back to the account administrator. The impact of this incident, however, seems to be negligible as until the time of writing this story, only one transaction was recorded (accounting to $0.78) in the public ledger of bitcoin with the addresses mentioned in the tweets.
Not the First Time
Earlier in July 2020, Bitcoin scammers carried out a high-profile hack that compromised nearly 130 Twitter accounts including verified accounts of known personalities like Jeff Bezos, Bill Gates, Elon Musk, Barack Obama, Joe Biden, and corporate accounts of Apple, Uber, and many more. It was a one of a kind hack, and ever since, it has been termed as “The Greatest Twitter Hack,” simply because multiple verified accounts were hacked simultaneously for scamming people. The FBI later arrested a 17-year-old, Graham Ivan Clark, a resident of Tampa, Florida, and pressed 30 counts of felony charges against him for perpetrating the Twitter hack. The cybercriminal and two of his accomplices earned more than $118,000 from this hack.










